A massive suspected Russian hacking campaign that compromised broad swathes of the federal government and private sector is being called a ‘cyber Pearl Harbor’ by members of both political parties.
The sprawling attack, which went undetected for nearly nine months, compromised the Departments of Homeland Security, Justice, Treasury, State and Energy, as well as a growing list of companies and local governments across the country.
Officials with the nation’s cybersecurity agency warn that the breach could be difficult to undo, saying the hackers ‘demonstrated sophistication and complex tradecraft’ and that it was likely that they had built additional secret backdoors while active inside the compromised networks.
The long-term planning of the attack became clear on Friday, as officials said that the hackers appeared to have conducted a dry run over a year ago, testing their ability to insert Trojan horse code into network management software from SolarWinds Corp, which was later used to compromise some 18,000 of the company’s customers.
“At this point, 425 out of the fortune 500 companies are effected and all five branches of the government,” cyber security expert Erik Knight told JimHeath.TV. “It’s very, very bad. Perhaps the worst ever.”
Rep. Jason Crow compared it to the attack on Pearl Harbor.
‘The situation is developing, but the more I learn this could be our modern day, cyber equivalent of Pearl Harbor,’ said Crow today. ‘Our nation is under assault. This cyberattack could be the largest in our history,’ he added, before slamming President Trump for his lack of public response to the cyber attack.
Senator Chris Coons, a Delaware Democrat, told MSNBC: ‘It’s pretty hard to distinguish this from an act of aggression that rises to the level of an attack that qualifies as war.’
Coons, 57, called the attack ‘as destructive and broad scale an engagement with our military systems, our intelligence systems as has happened in my lifetime.’
Trump has not yet said anything publicly about the intrusion.
He was being briefed ‘as needed,’ White House spokesman Brian Morgenstern told reporters on Friday.
Sen. Mitt Romney (R-UT) says the newly discovered massive hack was the high-tech equivalent of “Russian bombers repeatedly flying undetected over the entire country.”
And he is also blasting Trump for not protesting or punishing Russia for it.
“Not to have the White House aggressively speaking out and protesting and taking punitive action is really quite extraordinary,” Romney said.
Romney also called the silence and inaction by Trump “inexcusable.”
He explained that while Russia was not dropping bombs, their hack showed “that our cyber warfare readiness is extraordinarily weak, that they think so little of our ability to fight back from a cyber standpoint that they do this with impunity.”
In short, he said it shows that “our national security is extraordinarily vulnerable.
Private security companies say that the breach bears the hallmarks of a Kremlin operation.
Some have pointed at the Russian hacking cell dubbed ‘Cozy Bear’ — though other experts argue that the tools and methods used in the new attack are different from any past breach, making attribution tricky.
‘At the moment, there are no technical links with previous attacks, so it may be an entirely new actor,’ security firm Kaspersy said in a blog post.
Meanwhile, Microsoft President Brad Smith called the attack a ‘moment of reckoning’ that ‘illuminates the ways the cybersecurity landscape continues to evolve and become even more dangerous.’
Microsoft, one of the thousands of companies to receive the malicious update, said it had notified more than 40 customers around the world whose networks were infiltrated by the hackers.
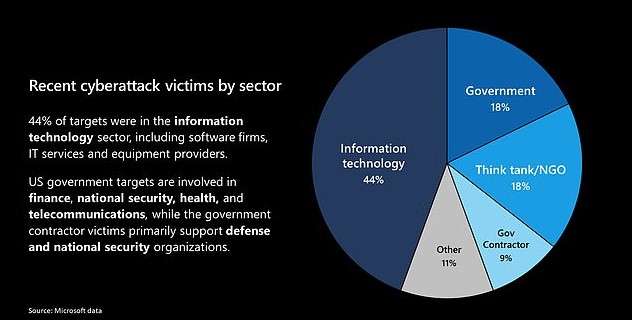
The list of victims includes not only government agencies, but security and other technology firms as well as think tanks and government contractors.
‘The attack unfortunately represents a broad and successful espionage-based assault on both the confidential information of the U.S. Government and the tech tools used by firms to protect them,’ Smith wrote in a blog post.
‘The coming months will present a critical test, not only for the United States but for other leading democracies and technology companies,’ he added.
On Friday, increasing evidence emerged showing that the hacking campaign had been carefully planned and executed over more than a year.
A version of the SolarWinds Orion product, which was ultimately used to deliver the SUNBURST backdoor to customer networks, was tampered with in October 2019 but did not contain the backdoor, according to the U.S. Cybersecurity and Infrastructure Security Agency.
The tampered files went undetected, and in March of 2020, the hackers began using Orion updates to deliver their backdoor.
‘We’re thinking they wanted to test whether or not it was going to work and whether it would be detected. So it was more or less a dry run,’ a source familiar with the investigation told Yahoo News.
‘They took their time. They decided to not go out with an actual backdoor right away. That signifies that they’re a little bit more disciplined and deliberate,’ the person added.
SolarWinds, which disclosed its unwitting role at the center of the global hack on Monday, has said that up to 18,000 users of its Orion software downloaded a compromised update containing malicious code planted by the attackers.
The attack was believed to be the work of an ‘outside nation state,’ SolarWinds said in a regulatory disclosure.
In addition to major federal agencies and critical infrastructure, the hackers targeted entities as various as a county government in Arizona and a cable television company.
The Pima County, Arizona government and Cox Communications Inc were identified as victims of the intrusion by Reuters after running a publicly available coding script.
The hack began as early as March this year when hackers snuck malicious code into recent versions of SolarWinds’ premier software product, Orion.
The popular software tool helps organizations monitor the performance of their computer networks and servers.
Hackers managed to install a secret network backdoor – which authorities are calling SUNBURST – into Orion’s software updates.
Its centralized monitoring looks for problems in an organization’s computer networks, which means that breaking in gave the attackers a ‘God-view’ of those networks.
It is not yet clear how hackers managed to infiltrate SolarWinds and go undetected for nine months.
During this time-frame, as many as 18,000 SolarWinds customers – including federal agencies and major companies – downloaded the compromised updates that contained the back door.
The software update became an instrument for hackers to steal information undetected for nine months.
Once installed on a network, the malware used a protocol designed to mimic legitimate SolarWinds traffic to communicate with a domain that has since been seized and shut down, the Cybersecurity and Infrastructure Security Agency has since revealed.
The initial contact domain would often direct the malware to a new internet protocol (IP) address for command and control. The attackers used rotating IPs and virtual private servers with IP addresses in the target’s home country to make detection of the traffic more difficult.
CISA said that once inside a network, the hackers focused on gathering information and frequently targeted the emails of IT and security staff to monitor any countermeasures.
The hackers are feared to have had access to government emails as far back as June.
Before this week, few people were aware of SolarWinds, the Austin-based software company providing vital computer network monitoring services to major corporations and government agencies worldwide.
But the revelation that elite cyber spies have spent months secretly exploiting SolarWinds’ software to peer into computer networks has put many of its highest-profile customers in national governments and Fortune 500 companies on high alert.
It’s also raising questions about whether company insiders knew of its security vulnerabilities as its biggest investors sold off stock.
A SolarWinds SEC filing from December 7 – just days prior to the hack emerging -revealed that the company’s board had appointed a replacement CEO.
SolarWinds’ longtime CEO, Kevin Thompson, had months earlier indicated that he would be leaving at the end of the year as the company explored spinning off one of its divisions.
The SolarWinds board appointed his replacement, current PulseSecure CEO Sudhakar Ramakrishna, on December 7, according to the financial filing.
It was also on December 7 that the company’s two biggest investors, Silver Lake and Thoma Bravo, which control a majority stake in the publicly traded company, sold more than $280 million in stock to a Canadian public pension fund.
The two private equity firms in a joint statement said they ‘were not aware of this potential cyberattack’ at the time they sold the stock.
The breach of SolarWinds’ software was first discovered by one of its customers: The prominent cybersecurity firm FireEye.
The California-based cyber security firm, which is also a government contractor, noticed a suspicious log-in on its network around December 8.
FireEye says the attackers stole some of its ‘red team’ software, which mimics cyber-attacks to test the security of its clients’ computers.
Two lawmakers, who were briefed on the hack this week, told Politico that FireEye representatives said that one of their employees had apparently been duped into revealing their two-factor authentication security details.
Company officials have denied the account given by congressional staffers and said none of its employees were tricked.
FireEye said they caught the breach when hackers tried to register a new device on its systems, which tipped the company off to the wider cyber-attack.
Following an investigation, FireEye say they determined that SolarWinds’ Orion software had been hacked.
‘We initially detected the incident because we saw a suspicious authentication to our VPN solution,’ a spokesperson has since said.
‘The attacker was able to enroll a device into our multi-factor authentication solution, and that generates an alert which we then followed up on.’
They insist that the SolarWinds breach was the source of the attack against FireEye.
Once it determined that there was a wider cyber-attack, a FireEye executive alerted SolarWinds on December 12 of the compromise.
After learning of the SolarWinds breach, the National Security Council held an emergency meeting at the White House on December 12.
The Cybersecurity and Infrastructure Security Agency and the FBI were brought in to investigate after some government agencies were confirmed to have been hacked.
At this time, people with knowledge of the meeting reported that hackers believed to be working for Russia had been monitoring internal email traffic at the US Treasury and Commerce departments.
Sources told Reuters that they feared the hacks uncovered so far may have been be the tip of the iceberg.
SolarWinds began alerting about 33,000 of its customers on December 13 that an ‘outside nation state’ – widely suspected to be Russia – had injected malicious code into some updated versions of its premier product, Orion.
The company said in a statement that updates to its monitoring software released between March and June of this year may have been subverted by what it described as a ‘highly-sophisticated, targeted and manual supply chain attack by a nation state’.
The Cybersecurity and Infrastructure Security Agency issued an emergency directive ordering federal agencies to ‘disconnect or power down’ the SolarWinds Orion software due to the breach.
The list of victims continues to grow from the cyberattack that is being described as the biggest hack in American history.
The two US agencies responsible for maintaining America’s nuclear weapons stockpile – Energy Department and the National Nuclear Security Administration – have already said they were compromised in the attack.
The attack also breached the Pentagon, FBI, Treasury and State Departments.
The DOE and the NNSA have warned Congress that their breached networks may include the Los Alamos National Laboratory, which conducts the government’s most sensitive and advanced nuclear research, Politico reported.
The US has an estimated 5,800 nuclear warheads, some of which are on missiles and bombs ready for launch from submarines, airplanes and land-based missiles, while others are held in storage. Most however are in storage, retired, or being decommissioned.
Their status is one of the government’s most closely-guarded secrets, as are efforts to create new weapons, which are part of the Los Alamos National Laboratory’s work.
Another attack was found in a field office of the Energy Department in Richland, Washington state, which Politico reported could have been an effort to gather information on how to disrupt the national electricity grid.
The sprawling attack also compromised broad swathes of the private sector, including Microsoft and likely most of the Fortune 500.
The true scale of who has been affected and what information has been stolen may never be known, officials and experts say.